After a week of this 0-day vulnerability being reported a number of posts have been published over the last few days detailing the disassembled malicious flash (swf) file exposing the invalid byte triggering the vulnerability. The vulnerability is caused when handling a “newfunction” instruction by Adobe’s ActionScript Virtual Machine 2 (AVM2). The vulnerability lies in both Adobe Reader and Adobe Flash so either product is vulnerable to attack. This post Im focusing on the actual malware that gets dropped when a malicious pdf file is opened.
After the pdf file is opened the first thing it does is process the malformed flash file in the pdf file which triggers the vulnerability dropping an executable in the root.
C:\-.exe
This file has been embedded in the pdf file making it portable without depending on any external sites to download and execute the malware. Once the dropped executable gets executed and a further 3 more files gets dropped onto the system.
C:\WINDOWS\EventSystem.dll
C:\WINDOWS\system32\es.ini
C:\WINDOWS\system32\dllcache\qmgr.dll
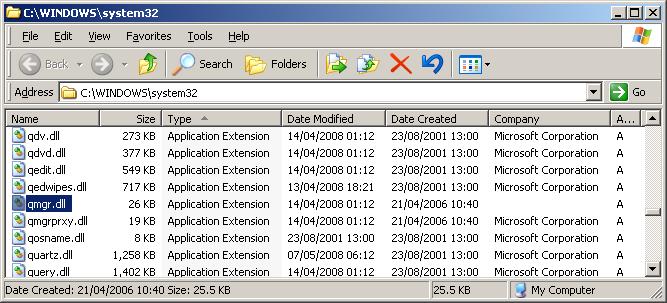
The original qmgr.dll file located in C:\WINDOWS\system32\ gets renamed to kernel64.dll and a malicious qmgr.dll takes it place. Also the original qmgr.dll file located in C:\WINDOWS\ServicePackFiles\i386\ gets replaced with the malicious qmgr.dll. The file Eventsystem.dll is a copy of the malicious dll file qmgr.dll and the file es.ini is just ascii file contains the text below used by qmgr.dll
[qmgrConfig]
ServerAddress=hxxp://210.211.31.214/ddradmin/ddrh.ashx
SleepTime=1000
Guid=00000000-0000-0000-0000-000000000000
The final change to the system making sure the malware starts up everytime is changing the settings in a legitimate Windows service called “Background Intelligent Transfer Service” (BITS). By default the status is not started and startup type set to manual. This now becomes a started status with the startup type set to automatic. Thereafter when the system starts the service dll qmgr.dll gets loaded in memory when the BITS service is started.
Note that the time stamp has also been modified making it harder to trace if searching by date.
Adobe has now released an update for Adobe Flash 10.1.53.64 fixing the vulnerability. This resolves the issue if a swf file is opened via the web. For pdf files Adobe Reader update has not yet been released. One way to mitigate for now is to rename the following files:
C:\Program Files\Adobe\Reader 9.0\Reader\authplay.dll
C:\Program Files\Adobe\Reader 9.0\Reader\rt3d.dll
This analysis had been done using Adobe Reader version 9.3.2 with a pdf file having a md5 hash value of 721601bdbec57cb103a9717eeef0bfca
References:
http://secunia.com/advisories/40026/
http://www.kb.cert.org/vuls/id/486225/
http://www.adobe.com/support/security/bulletins/apsb10-14.html
http://www.adobe.com/support/security/advisories/apsa10-01.html
http://www.symantec.com/connect/blogs/analysis-zero-day-exploit-adobe-flash-and-reader
http://community.websense.com/blogs/securitylabs/archive/2010/06/09/having-fun-with-adobe-0-day-exploits.aspx