Recently I’ve been researching into ActiveX controls in Office documents as I had some ideas I wanted to test out after reading Dominic Wang’s paper “Understanding Microsoft Word OLE Exploit Primitives: Exploiting CVE-2015-1642 Microsoft Office CTaskSymbol Use-After-Free Vulnerability” [1] and Haifei Li’s and Bing Sun’s presentation slides “Attacking Interoperability: An OLE Edition” [2].
Some vulnerabilities that have been exploited in the past (CVE-2013-3906, CVE-2015-2424, CVE-2015-1641) have been embedding ActiveX controls to perform the heap spray whether be in Open XML format or encapsulated in RTF format. During my tests it was obvious that spraying the heap just took ages, waiting sometimes minutes before triggering the vulnerability. The exploits I examined either used one large ActiveX1.bin file or multiple ActiveX[x].bin files. This post just shows how we can spray the heap in seconds rather than minutes, mainly working with MS Word documents on a fully patched Windows 7 32bit with Office Professional 2010 with Open XML formatted files.
Office Open XML structure
I started looking into an Open XML formatted document which is basically a zip archive so just by renaming the extension to a zip we can extract, make changes to the files and zip it up again. Running the tree command in the extracted folder of a simple Word document we see the files listed below which contains one ActiveX object.
| [Content_Types].xml
|
+---docProps
| app.xml
| core.xml
|
+---word
| | document.xml
| | fontTable.xml
| | settings.xml
| | styles.xml
| | stylesWithEffects.xml
| | webSettings.xml
| |
| +---activeX
| | | activeX1.bin
| | | activeX1.xml
| | |
| | \---_rels
| | activeX1.xml.rels
| |
| +---media
| | image1.wmf
| |
| +---theme
| | theme1.xml
| |
| \---_rels
| document.xml.rels
|
\---_rels
.rels
activeX1.bin is our Compound Document Format file which would contain our sprayed data and activeX1.xml would contain our classid to be used. When adding or removing ActiveX objects manually there are 5 files you’ll need to update
[Content_Types].xml – contains entries pointing to individual activeX[x].xml entries
document.xml – contains ids which refer activex[x].xml files set in document.xml.rels
document.xml.rels – contains individual image[x].wmf and activeX[x].xml entries, unique rIds
activeX[x].xml – Calls classIDs in each activeX[x].xml files
activeX[x].xml.rels – Points to individual activeX[x].bin files
activeX[x].bin – Compound File Binary Format
Here we could modify activeX[x].xml.rels to point to the same ActiveX1.bin compound document file as normally Office creates multiple unique activeX[x].bin files. This would reduce our total file size, save some seconds at spray time and just easy to manage.
Compound File Binary Format
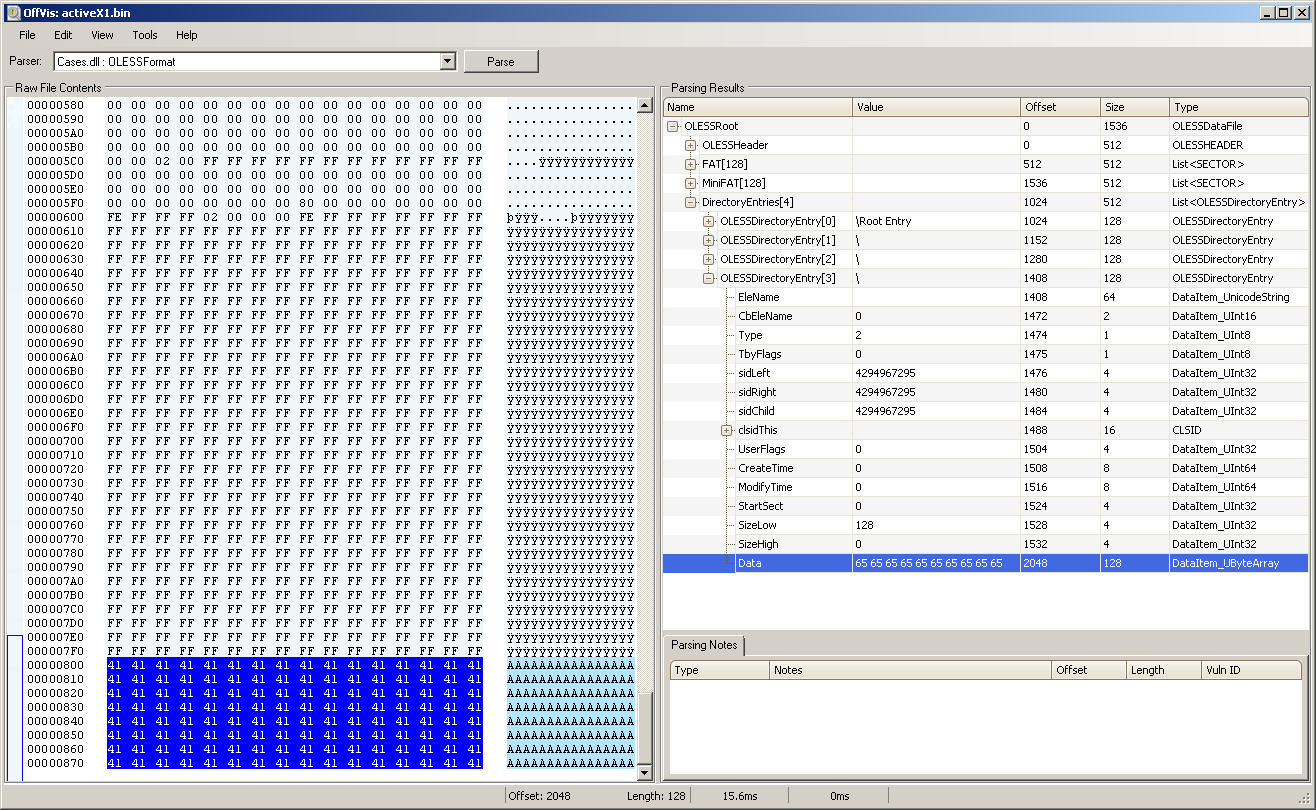
Using Microsoft’s Office Visualization Tool (OffVis) we can deconstruct the compound document file activeX1.bin in order to understand its structure and values. The Microsoft specifications document [3] explains everything you need to know about the format.
A compound file is a structure for storing a file system, similar to a simplified FAT file system inside a single file, by dividing the single file into sectors. It is capable of storing data that is structured as storage and streams.
Viewing our activeX1.bin file which is this case the classid is instantiating Flash. Here in the OLESSDirectoryEntry[0] section we could null out the values of the clsidThis field as when the document is opened the classid is read from our ActiveX[x].xml file. Another entry we could null out is the ModifyTime field values. One important field is Object Type. This field MUST be 0x00, 0x01, 0x02, or 0x05, depending on the actual type of object.
Unknown or unallocated 0x00
Storage Object 0x01
Stream Object 0x02
Root Storage Object 0x05
Non-root directory entries are normally marked as either stream or storage elements. So leaving OLESSDirectoryEntry[0] entry alone as Type 5 the other directory entries OLESSDirectoryEntry[1] OLESSDirectoryEntry[2] and OLESSDirectoryEntry[3] we could be changed to Type 0. Once Type changed to 0 the Data entry in OffVis dissappears, also SizeLow field values can then also be nulled. The SizeLow and SizeHigh fields represent the stream size (8 bytes). This 64-bit integer field contains the size of the user-defined data, if this is a stream object. For a root storage object, this field contains the size of the mini stream.
The benefit of these changes is that we can remove any unwanted data at the end and just have an ActiveX1.bin file of only 2048 bytes. As for nulling out clsidThis and ModifyTime fields just removes any reference to the classid or time modified. If we wanted to say encapsulate our sprayed data we could change the Type object value to 2 and SizeLow value as you can see below but not really necessary so no need to complicate stuff. when it comes to the spraying our data I noticed all we need to do is just append our sprayed data to our 2048 bytes compound file without making any further changes. This is enough to load it in memory.
Class IDs to use
Now the question comes to what classIDs do we use for our heap spray? ClassIDs are set in the ActiveX[x].xml files where then the associated libraries loads. After experimenting with different classids I realised any classID could be used, depending on what classID is being called affects the performance drastically.
For example exploits CVE-2013-3906 or CVE-2015-1641 used classID {1EFB6596-857C-11D1-B16A-00C0F0283628} (MSComctlLib.TabStrip.2). This refers to library C:\Windows\system32\MSCOMCTL.OCX which is 1,070,232 bytes in size. This library is huge so the amount of time to spray accumulates on how many chunks being sprayed. So if I used a classID which referred to a library of a small file size the spray time reduced drastically. Taking it a step further, it was discovered that using a non-existing classID could be used such as {00000000-0000-0000-0000-000000000001}. Since this classID does not exist on the system there would be no referring library to load so in theory would further reduce the spray time. During tests this proved to be the case and heap spraying was successful and the time was further reduced.
The activeX[x].xml file would normally look like this
<?xml version='1.0' encoding='UTF-8' standalone='no'?>
<ax:ocx ax:classid='{00000000-0000-0000-0000-000000000001}'
ax:persistence='persistStorage' r:id='rId1'
xmlns:ax='http://schemas.microsoft.com/office/2006/activeX'
xmlns:r='http://schemas.openxmlformats.org/officeDocument/2006/relationships'/>
Heap Spraying times
To get an idea of what kind of times we are dealing with, MetaSploit’s TIFF Integer Overflow exploit [4] was used which uses ActiveX to spray the heap with 591 chunks using the classid {1EFB6596-857C-11D1-B16A-00C0F0283628} referring to MSCOMCTL.OCX library. To spray the heap it took around 1 minute 10 seconds. Now replacing the classid with {00000000-0000-0000-0000-000000000001} it took only around 6 seconds which is a huge difference.
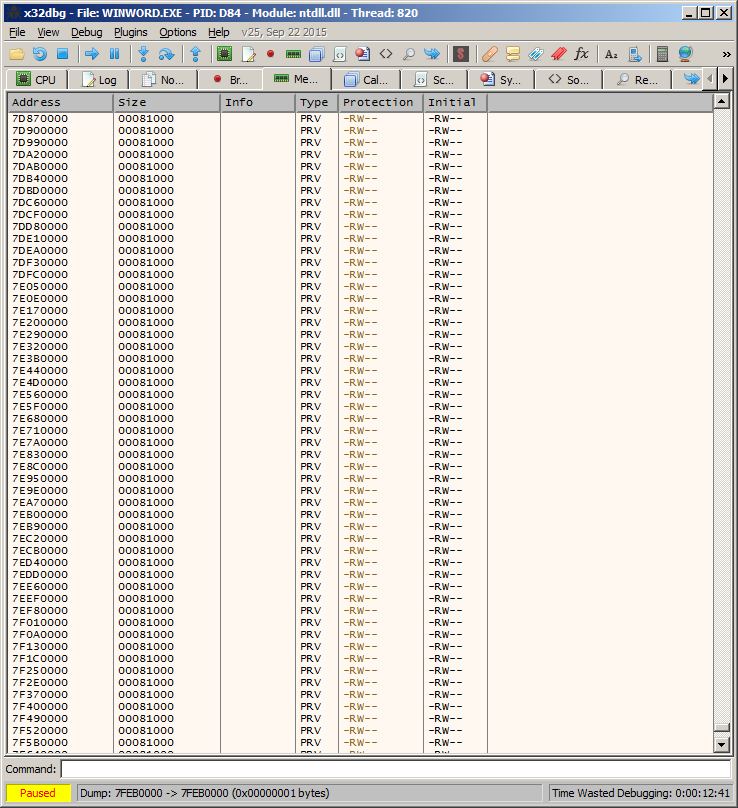
The table below shows the times it takes to spray, memory addresses sprayed upto and memory allocated based on the number of chunks. These figures will vary but it just gives you an idea.
The size of the activeX1.bin file used on Office 2010 32bit was 514KB which takes a chunk size of 0x81000 (528384 bytes) in memory.
526,336 bytes = 2048 (header) + 1024 (block size) * 512 (no. of blocks)
| Chunks | Time to spray | Memory spray to | Memory allocated |
| 500 | 5 seconds | 0x16450000 | 300 mb |
| 1000 | 10 seconds | 0x28DD0000 | 575 mb |
| 2000 | 20 seconds | 0x4D3A0000 | 1.1 gb |
| 4000 * | 58 seconds | 0x7FEB0000 | 2 gb |
* This high number of chunks might not work and document will not properly open.
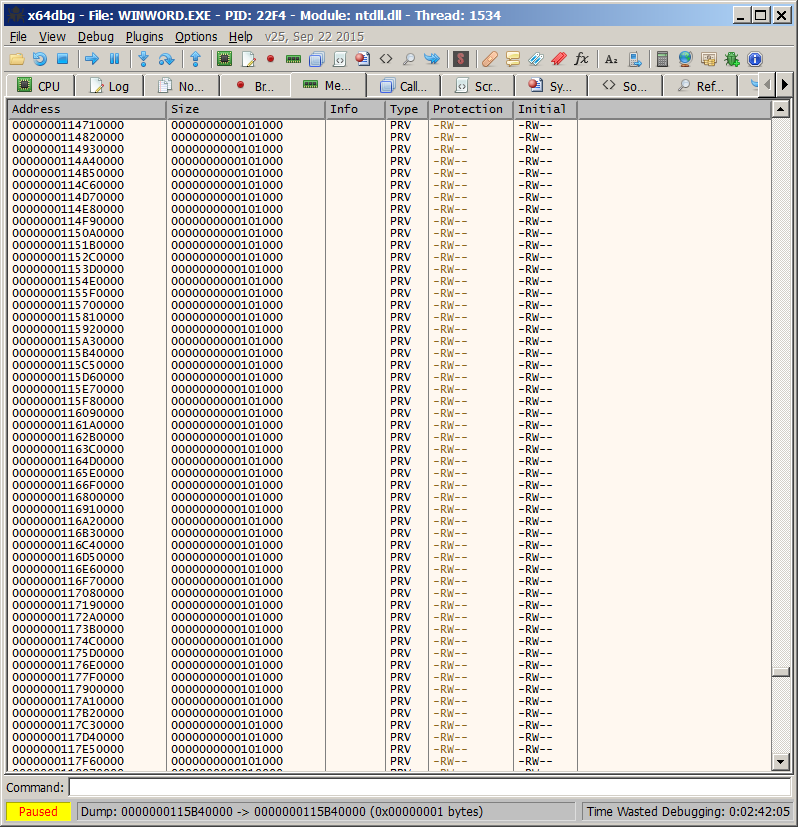
The size of the activeX1.bin file used on Office 2010 64bit was 1026KB which takes a chunk size of 0x101000 (1052672 bytes) in memory.
1,050,624 bytes = 2048 (header) + 1024 (block size) * 1024 (no. of blocks)
| Chunks | Time to spray | Memory spray to | Memory allocated |
| 500 | 5 seconds | 0x0000000027dc0000 | 583 mb |
| 1000 | 12 seconds | 0x000000004a2f0000 | 1.1 gb |
| 2000 | 27 seconds | 0x000000008f450000 | 2.1 gb |
| 4000 | 120 seconds | 0x0000000117910000 | 4 gb |
Memory allocated on Windows 7 32bit with Office 2010 32bit
Memory allocated on Windows 7 64bit with Office 2010 64bit
Mitigation
Spraying the heap using classids that do not exist on the system prevents a number of mitigations. So disabling ActiveX controls in Microsoft Office via the Trust Center settings or via Office kill bit in the registry are ineffective. Only using Microsoft EMET’s heap spray mitigation would provide some protection.
Summary
To get the fastest spray possible the main points to take away is
1. Use one ActiveX1.bin compound document file
2. Use a smaller ActiveX1.bin file with more xmls calling it
3. Use a classID that doesn’t exist on the system
All my Word document spray files and perl scripts you can download from here. When creating your own documents with the scripts just extract a existing document and overwrite with the files created by the scripts.
References
[1] https://www.nccgroup.trust/uk/our-research/understanding-microsoft-word-ole-exploit-primitives
[2] https://www.blackhat.com/docs/us-15/materials/us-15-Li-Attacking-Interoperability-An-OLE-Edition.pdf [PDF]
[3] https://msdn.microsoft.com/en-gb/library/dd942138.aspx
[4] https://www.rapid7.com/db/modules/exploit/windows/fileformat/mswin_tiff_overflow